iGPT vs Threat Watch
Side-by-side comparison to help you choose the right product.
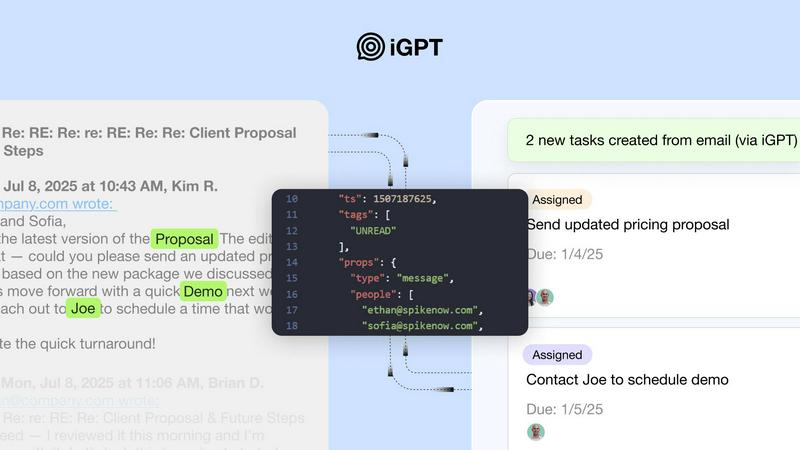
iGPT transforms email data into actionable insights, streamlining enterprise workflows with context-aware intelligence.
Last updated: February 28, 2026
Threat Watch
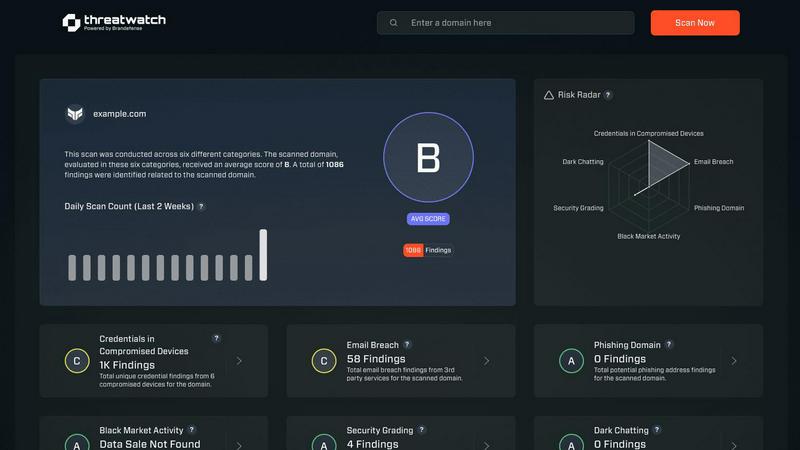
Quickly gauge your cybersecurity health and gain insights to strengthen your defenses against evolving threats.
Last updated: March 1, 2026
Visual Comparison
iGPT
Threat Watch
Feature Comparison
iGPT
Immediate Integration
iGPT provides an SDK and a live playground, enabling users to test requests and responses quickly. This immediate integration capability allows businesses to seamlessly incorporate iGPT into their existing systems without lengthy setup times.
Unified Endpoint
With iGPT, users can send a single request that performs retrieval, context shaping, and reasoning all in one pipeline. This unified approach simplifies the interaction with multiple data sources, allowing for more efficient data retrieval and processing.
Contextual Responses
Responses generated by iGPT are ready for reasoning and automation, complete with citations to the original source. This feature ensures that users can trust the information provided and trace back to the origins of data, enhancing transparency and accountability.
Hybrid Retrieval
iGPT employs a hybrid retrieval method that combines semantic, keyword, and filter-based searches, scoring and reranking results in a single call. This advanced feature improves the relevance and accuracy of the information retrieved, ensuring users receive the most pertinent insights.
Threat Watch
Comprehensive Asset Evaluation
Threat Watch provides an exhaustive analysis of your organization's digital assets, identifying vulnerabilities and exposures that could be exploited by cybercriminals. This feature empowers organizations to understand their risk profile comprehensively.
Real-Time Threat Monitoring
With continuous monitoring capabilities, Threat Watch keeps an eye on critical security categories, including compromised devices and breached accounts. This ensures that organizations can detect potential threats as they arise and respond promptly.
Dark Web Intelligence
Threat Watch's dark web content monitoring feature allows organizations to uncover potential threats lurking in hidden corners of the internet. By identifying compromised credentials and sensitive information, businesses can take proactive measures to protect their assets.
Phishing Detection and Prevention
The platform includes robust phishing address tracking, enabling organizations to identify and neutralize phishing attempts before they can cause harm. This feature enhances the security posture by significantly reducing the risk of successful phishing attacks.
Use Cases
iGPT
Email Assistants
iGPT can be utilized to build intelligent agents that draft, prioritize, and act on emails with full context. This application enhances team collaboration and accelerates response times, enabling organizations to streamline their communication processes.
Workflow Automation
By turning email threads into actionable tasks, deadlines, and approvals, iGPT helps organizations automate their workflows. This use case minimizes bottlenecks and ensures that important items are flagged and addressed promptly.
Support Copilots
iGPT assists in reconstructing complete customer stories across lengthy email chains, attachments, and shifts in tone. This capability enhances customer support efforts, allowing teams to understand and address customer needs more effectively.
Insights from Attachments
The tool can summarize critical information from invoices, contracts, and other documents within the context of the relevant email thread. This feature enables businesses to extract actionable insights quickly and make informed decisions based on comprehensive data.
Threat Watch
Protecting Sensitive Data
Organizations can leverage Threat Watch to safeguard sensitive customer and business data by continuously monitoring for signs of data breaches and compromised accounts, ensuring compliance and trust.
Enhancing Incident Response
Security teams can utilize the real-time insights provided by Threat Watch to enhance their incident response strategies. By understanding the current threat landscape, they can act swiftly and effectively during security incidents.
Mitigating Phishing Risks
With its phishing detection capabilities, Threat Watch serves as a critical tool for organizations looking to mitigate the risks associated with phishing attacks. By identifying phishing addresses early, companies can protect their employees and customers.
Monitoring Dark Web Activity
Threat Watch enables organizations to stay one step ahead of cyber threats by monitoring dark web activity for compromised credentials. This proactive surveillance allows businesses to take necessary actions before any potential exploitation occurs.
Overview
About iGPT
iGPT is an advanced email intelligence API that revolutionizes how enterprises manage their email and communication data. Designed specifically for organizations that rely heavily on email for operational workflows, iGPT offers a secure and auditable gateway for AI-powered systems to access, comprehend, and utilize email content effectively. By extracting valuable insights from email communications, iGPT empowers businesses to enhance their decision-making processes while maintaining compliance and security. The tool features immediate integration capabilities, context-aware responses, and enterprise-grade security measures, ensuring that organizations can leverage their existing data without compromising on safety. As a result, iGPT streamlines email management, automates routine tasks, and allows teams to focus on strategic initiatives, thereby driving productivity and operational efficiency.
About Threat Watch
Threat Watch is a state-of-the-art cybersecurity intelligence solution meticulously crafted to protect organizations from the dynamic landscape of cyber threats. By harnessing the power of advanced analytics, Threat Watch assesses your organization's assets, vulnerabilities, and exposures to deliver a holistic view of your cyber health. This platform is tailored for businesses of all sizes, from small startups to large enterprises, as it enhances the capabilities of security teams by providing real-time insights that accelerate decision-making and foster effective risk mitigation strategies. With continuous monitoring of critical security categories such as compromised devices, breached accounts, phishing addresses, and dark web content, Threat Watch adopts a proactive approach. This enables organizations to swiftly identify potential threats and prioritize their responses with precision. The main value proposition of Threat Watch lies in its ability to streamline cybersecurity efforts, ultimately bolstering organizational resilience against an increasingly intricate threat landscape. By leveraging Threat Watch, companies can uncover their cybersecurity health rapidly and stay ahead of emerging threats, ensuring a safer digital environment for their operations.
Frequently Asked Questions
iGPT FAQ
How does iGPT ensure data security?
iGPT implements enterprise-grade security measures, including zero data training, role-based access control, and zero data retention. This ensures that user data is never used for model training and that all processing occurs in a secure environment.
Can iGPT integrate with existing email systems?
Yes, iGPT is designed for immediate integration with existing email systems through its SDK and API. This allows organizations to leverage their current workflows while incorporating advanced email intelligence.
What types of responses can iGPT generate?
iGPT generates context-aware responses that are ready for reasoning and automation. Each response includes citations back to the original email or attachment, ensuring that users can verify the information provided.
How quickly can businesses expect to see results with iGPT?
Businesses can expect to see results rapidly, with retrieval times around 200 milliseconds and responses available shortly after. The swift processing capabilities of iGPT enable teams to act on insights quickly, enhancing overall productivity.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for businesses of all sizes, from small startups to large enterprises, providing tailored solutions to enhance cybersecurity preparedness across various sectors.
How does Threat Watch monitor compromised devices?
Threat Watch continuously scans and evaluates devices connected to your network, identifying any that may have been compromised by malware or unauthorized access, ensuring swift remediation actions.
Is Threat Watch suitable for organizations with limited cybersecurity resources?
Yes, Threat Watch is ideal for organizations with limited resources, as it streamlines cybersecurity efforts and provides actionable insights that empower teams to make informed decisions quickly.
How does Threat Watch help improve overall cybersecurity health?
By offering comprehensive asset evaluations, real-time monitoring, and dark web intelligence, Threat Watch equips organizations with the tools needed to understand and enhance their cybersecurity posture effectively.
Alternatives
iGPT Alternatives
iGPT is an advanced email intelligence API that enhances how enterprises manage their email communications and data. By providing a secure and intelligent gateway for accessing and understanding email content, iGPT enables organizations to derive valuable insights from their communication flows. As businesses evolve and their needs change, users often find themselves exploring alternatives to iGPT due to factors such as pricing, specific feature requirements, or platform compatibility. When searching for an alternative to iGPT, it's essential to consider several factors. Look for APIs that offer seamless integration, robust security, and the ability to deliver context-aware insights. Assessing features such as real-time processing, thread reconstruction, and hybrid retrieval can help ensure that the chosen solution aligns with your organization's operational workflows and enhances productivity.
Threat Watch Alternatives
Threat Watch is a sophisticated cybersecurity intelligence solution designed to help organizations assess their cybersecurity health and enhance their defenses against a myriad of evolving cyber threats. By utilizing advanced analytics, it provides a comprehensive evaluation of assets, vulnerabilities, and exposures, making it an invaluable tool for businesses of any size striving to protect their digital environments. Users often seek alternatives to Threat Watch due to factors such as pricing, specific feature sets, or compatibility with existing platforms. When searching for an alternative, it is essential to consider the unique needs of your organization, including the level of protection required, ease of use, scalability, and the responsiveness of customer support. Evaluating these metrics will help ensure that the chosen solution aligns effectively with your cybersecurity objectives.
