Threat Watch
Quickly gauge your cybersecurity health and gain insights to strengthen your defenses against evolving threats.
Visit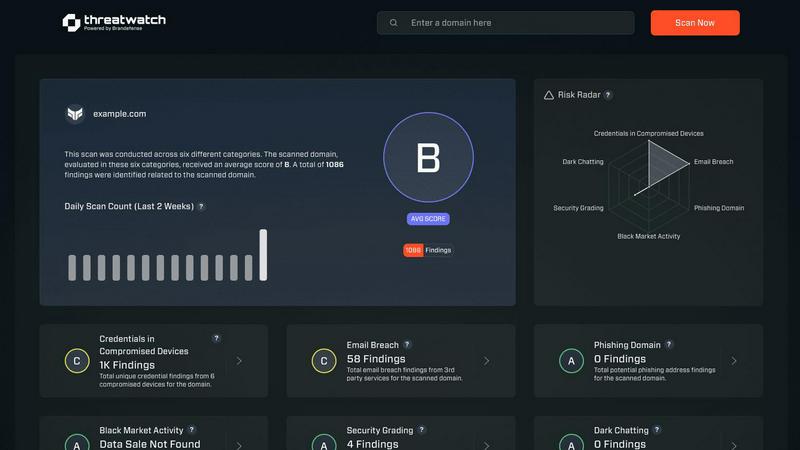
About Threat Watch
Threat Watch is a state-of-the-art cybersecurity intelligence solution meticulously crafted to protect organizations from the dynamic landscape of cyber threats. By harnessing the power of advanced analytics, Threat Watch assesses your organization's assets, vulnerabilities, and exposures to deliver a holistic view of your cyber health. This platform is tailored for businesses of all sizes, from small startups to large enterprises, as it enhances the capabilities of security teams by providing real-time insights that accelerate decision-making and foster effective risk mitigation strategies. With continuous monitoring of critical security categories such as compromised devices, breached accounts, phishing addresses, and dark web content, Threat Watch adopts a proactive approach. This enables organizations to swiftly identify potential threats and prioritize their responses with precision. The main value proposition of Threat Watch lies in its ability to streamline cybersecurity efforts, ultimately bolstering organizational resilience against an increasingly intricate threat landscape. By leveraging Threat Watch, companies can uncover their cybersecurity health rapidly and stay ahead of emerging threats, ensuring a safer digital environment for their operations.
Features of Threat Watch
Comprehensive Asset Evaluation
Threat Watch provides an exhaustive analysis of your organization's digital assets, identifying vulnerabilities and exposures that could be exploited by cybercriminals. This feature empowers organizations to understand their risk profile comprehensively.
Real-Time Threat Monitoring
With continuous monitoring capabilities, Threat Watch keeps an eye on critical security categories, including compromised devices and breached accounts. This ensures that organizations can detect potential threats as they arise and respond promptly.
Dark Web Intelligence
Threat Watch's dark web content monitoring feature allows organizations to uncover potential threats lurking in hidden corners of the internet. By identifying compromised credentials and sensitive information, businesses can take proactive measures to protect their assets.
Phishing Detection and Prevention
The platform includes robust phishing address tracking, enabling organizations to identify and neutralize phishing attempts before they can cause harm. This feature enhances the security posture by significantly reducing the risk of successful phishing attacks.
Use Cases of Threat Watch
Protecting Sensitive Data
Organizations can leverage Threat Watch to safeguard sensitive customer and business data by continuously monitoring for signs of data breaches and compromised accounts, ensuring compliance and trust.
Enhancing Incident Response
Security teams can utilize the real-time insights provided by Threat Watch to enhance their incident response strategies. By understanding the current threat landscape, they can act swiftly and effectively during security incidents.
Mitigating Phishing Risks
With its phishing detection capabilities, Threat Watch serves as a critical tool for organizations looking to mitigate the risks associated with phishing attacks. By identifying phishing addresses early, companies can protect their employees and customers.
Monitoring Dark Web Activity
Threat Watch enables organizations to stay one step ahead of cyber threats by monitoring dark web activity for compromised credentials. This proactive surveillance allows businesses to take necessary actions before any potential exploitation occurs.
Frequently Asked Questions
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for businesses of all sizes, from small startups to large enterprises, providing tailored solutions to enhance cybersecurity preparedness across various sectors.
How does Threat Watch monitor compromised devices?
Threat Watch continuously scans and evaluates devices connected to your network, identifying any that may have been compromised by malware or unauthorized access, ensuring swift remediation actions.
Is Threat Watch suitable for organizations with limited cybersecurity resources?
Yes, Threat Watch is ideal for organizations with limited resources, as it streamlines cybersecurity efforts and provides actionable insights that empower teams to make informed decisions quickly.
How does Threat Watch help improve overall cybersecurity health?
By offering comprehensive asset evaluations, real-time monitoring, and dark web intelligence, Threat Watch equips organizations with the tools needed to understand and enhance their cybersecurity posture effectively.
Explore more in this category:
Similar to Threat Watch
Refine your brand identity instantly with our free AI tool that generates unique, catchy business names for startups and domains.
MarketWrk automates CPG pricing and MAP monitoring, delivering real-time alerts and insights to streamline your pricing strategy and boost sales.
Opal44 transforms your Google Analytics 4 data into clear, actionable insights in everyday language for smarter.
Fusedash continuously transforms raw data into clear dashboards so your team can act and improve.
finban simplifies liquidity planning, empowering confident decisions on hiring, taxes, and investments without Excel.
Zignt simplifies contract management with reusable templates, secure signing, and real-time collaboration for teams.
aVenture delivers AI-driven insights for researching private companies and tracking investments in an evolving market.
iGPT transforms email data into actionable insights, streamlining enterprise workflows with context-aware intelligence.
