CMMC ROI vs Threat Watch
Side-by-side comparison to help you choose the right product.
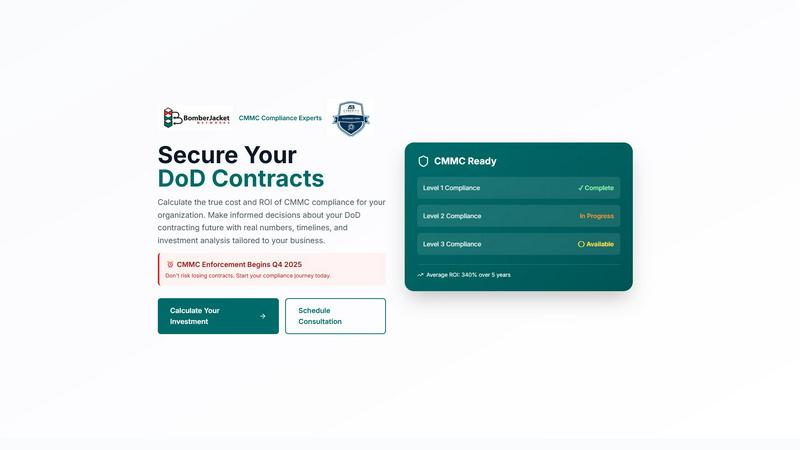
CMMC ROI
Calculate your CMMC compliance costs and ROI to secure your future DoD contracts.
Last updated: March 1, 2026
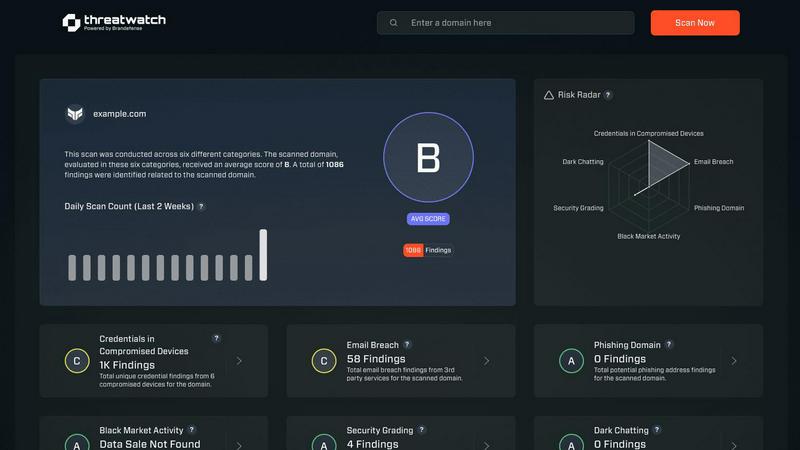
Threat Watch
Quickly gauge your cybersecurity health and gain insights to strengthen your defenses against evolving threats.
Last updated: March 1, 2026
Visual Comparison
CMMC ROI
Threat Watch
Feature Comparison
CMMC ROI
Personalized Investment Calculator
The core of the platform is a dynamic, editable calculator that tailors financial projections to your unique business profile. By adjusting parameters like company size, annual DoD revenue, target CMMC level, and current progress status, you generate a bespoke analysis of your estimated 5-year investment range, payback period, and overall ROI percentage, moving from generic estimates to a precise, actionable financial model for your compliance journey.
Detailed ROI Timeline Projection
This feature provides a visual, month-by-month breakdown of your investment and returns over a 5-year period. It clearly illustrates the cumulative expenditures and the point at which your investment breaks even, turning into positive returns. This cyclical view reinforces the long-term value of compliance, showing how initial costs are recouped and surpassed by protected contract revenue and avoided breach costs, supporting continuous strategic planning.
CMMC Protection & Risk Assessment
Beyond pure financials, the tool quantifies your operational risk exposure. It calculates the percentage of contract value at risk without certification, estimates the average cost of breaches and false claims avoided, and projects the competitive win-rate increase gained by being CMMC certified. This holistic view ensures your investment analysis is grounded in both financial protection and tangible business growth opportunities.
Implementation Timeline Estimator
Understanding the time commitment is crucial for planning. This feature outlines a typical 12-month iterative journey to CMMC Level 2 certification, breaking it into phases like Gap Assessment, Remediation, Documentation, and Assessment Prep. This structured timeline helps organizations sequence activities, allocate resources effectively, and maintain momentum through each phase of the continuous improvement cycle toward final certification.
Threat Watch
Comprehensive Asset Evaluation
Threat Watch provides an exhaustive analysis of your organization's digital assets, identifying vulnerabilities and exposures that could be exploited by cybercriminals. This feature empowers organizations to understand their risk profile comprehensively.
Real-Time Threat Monitoring
With continuous monitoring capabilities, Threat Watch keeps an eye on critical security categories, including compromised devices and breached accounts. This ensures that organizations can detect potential threats as they arise and respond promptly.
Dark Web Intelligence
Threat Watch's dark web content monitoring feature allows organizations to uncover potential threats lurking in hidden corners of the internet. By identifying compromised credentials and sensitive information, businesses can take proactive measures to protect their assets.
Phishing Detection and Prevention
The platform includes robust phishing address tracking, enabling organizations to identify and neutralize phishing attempts before they can cause harm. This feature enhances the security posture by significantly reducing the risk of successful phishing attacks.
Use Cases
CMMC ROI
Strategic Budget Justification for Leadership
CFOs and company executives can use the tool to build a compelling, data-backed business case for the necessary CMMC compliance budget. The detailed ROI projections and risk assessment translate complex security requirements into clear financial terms, securing executive buy-in and funding by demonstrating how the investment protects existing revenue and unlocks future contract opportunities.
Proposal and Bidding Strategy Development
Business development and capture teams can leverage the calculator to understand the compliance cost implications of pursuing specific DoD contracts requiring different CMMC levels. This allows for more accurate bidding, ensuring costs are accounted for, and strengthens proposals by showcasing the company's certified status and understanding of the compliance investment.
Compliance Program Planning and Phasing
For organizations beginning their CMMC journey, the tool helps create a phased, iterative implementation plan. By inputting "Not Started" status and seeing the full cost, teams can prioritize controls, schedule remediation activities based on the provided timeline, and allocate internal resources or budget for external consultants in a structured, efficient manner.
Progress Validation and Course Correction
Companies already "In Progress" with their compliance efforts can input their current status to receive adjusted cost estimates (reflecting a progress discount) and updated ROI figures. This allows for continuous assessment of the program's financial trajectory, validating that the investment is on track and enabling course correction if certain phases are over or under budget.
Threat Watch
Protecting Sensitive Data
Organizations can leverage Threat Watch to safeguard sensitive customer and business data by continuously monitoring for signs of data breaches and compromised accounts, ensuring compliance and trust.
Enhancing Incident Response
Security teams can utilize the real-time insights provided by Threat Watch to enhance their incident response strategies. By understanding the current threat landscape, they can act swiftly and effectively during security incidents.
Mitigating Phishing Risks
With its phishing detection capabilities, Threat Watch serves as a critical tool for organizations looking to mitigate the risks associated with phishing attacks. By identifying phishing addresses early, companies can protect their employees and customers.
Monitoring Dark Web Activity
Threat Watch enables organizations to stay one step ahead of cyber threats by monitoring dark web activity for compromised credentials. This proactive surveillance allows businesses to take necessary actions before any potential exploitation occurs.
Overview
About CMMC ROI
CMMC ROI is a strategic decision-making platform engineered for Department of Defense (DoD) contractors and subcontractors navigating the mandatory Cybersecurity Maturity Model Certification (CMMC) landscape. As enforcement is set to begin in Q4 2025, this tool transforms the complex, often daunting compliance journey into a clear, quantifiable business case. It provides a dynamic framework for calculating the true, multi-year investment and the substantial return on investment (ROI) associated with achieving and maintaining CMMC compliance across Levels 1, 2, and 3. By inputting specific organizational data—such as company size, DoD revenue, and current compliance status—users receive personalized financial projections, including total investment ranges, payback periods, and a detailed ROI timeline. This empowers leaders to move beyond viewing CMMC as a mere cost center and instead see it as a critical investment in contract security, risk mitigation, and competitive advantage. The tool fosters a mindset of continuous improvement, enabling organizations to iteratively assess their posture, plan their investments, and secure their future in the DoD supply chain with data-driven confidence.
About Threat Watch
Threat Watch is a state-of-the-art cybersecurity intelligence solution meticulously crafted to protect organizations from the dynamic landscape of cyber threats. By harnessing the power of advanced analytics, Threat Watch assesses your organization's assets, vulnerabilities, and exposures to deliver a holistic view of your cyber health. This platform is tailored for businesses of all sizes, from small startups to large enterprises, as it enhances the capabilities of security teams by providing real-time insights that accelerate decision-making and foster effective risk mitigation strategies. With continuous monitoring of critical security categories such as compromised devices, breached accounts, phishing addresses, and dark web content, Threat Watch adopts a proactive approach. This enables organizations to swiftly identify potential threats and prioritize their responses with precision. The main value proposition of Threat Watch lies in its ability to streamline cybersecurity efforts, ultimately bolstering organizational resilience against an increasingly intricate threat landscape. By leveraging Threat Watch, companies can uncover their cybersecurity health rapidly and stay ahead of emerging threats, ensuring a safer digital environment for their operations.
Frequently Asked Questions
CMMC ROI FAQ
How accurate are the cost estimates provided by the CMMC ROI calculator?
The calculator provides realistic ranges based on typical implementation scenarios for companies of different sizes and compliance levels. While it offers a highly accurate starting point for financial planning, the final investment can vary based on your specific IT environment, existing security controls, and chosen implementation partners. It is designed to be an iterative planning tool; you should refine the estimates with detailed quotes from CMMC consultants as your plan matures.
What is included in the "Protected Value" used to calculate ROI?
The Protected Value is a key metric representing the financial benefit of certification. It combines your organization's total 5-year DoD contract revenue (which is at risk without certification) with an estimated average cost avoidance of $2.5M for potential data breaches and False Claims Act penalties. This holistic approach captures both the preservation of existing income and the mitigation of significant potential losses.
My company is already partially compliant. How does the tool account for this?
The calculator includes a "Current Compliance Status" selector with options like "Not Started," "In Progress," and "Nearly Complete." Selecting "In Progress" applies a 30% discount to the implementation cost estimate, while "Nearly Complete" applies a 60% discount. This feature allows for iterative refinement of your financial model as you progress, ensuring your ROI projection reflects your actual starting point and ongoing investment.
Why is the payback period often shown to be relatively short, even with large investments?
The payback period—the time it takes for the returns to equal the initial investment—is frequently under one year because the primary "return" is the protection of very large, existing DoD contract revenues that would be completely lost without certification. The tool models the high immediate risk of contract forfeiture against the upfront compliance cost, demonstrating that the investment is fundamentally about securing current and future revenue streams.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for businesses of all sizes, from small startups to large enterprises, providing tailored solutions to enhance cybersecurity preparedness across various sectors.
How does Threat Watch monitor compromised devices?
Threat Watch continuously scans and evaluates devices connected to your network, identifying any that may have been compromised by malware or unauthorized access, ensuring swift remediation actions.
Is Threat Watch suitable for organizations with limited cybersecurity resources?
Yes, Threat Watch is ideal for organizations with limited resources, as it streamlines cybersecurity efforts and provides actionable insights that empower teams to make informed decisions quickly.
How does Threat Watch help improve overall cybersecurity health?
By offering comprehensive asset evaluations, real-time monitoring, and dark web intelligence, Threat Watch equips organizations with the tools needed to understand and enhance their cybersecurity posture effectively.
Alternatives
CMMC ROI Alternatives
CMMC ROI is a specialized business intelligence tool designed to help Department of Defense contractors calculate the costs and return on investment for achieving Cybersecurity Maturity Model Certification. It provides a data-driven framework for planning compliance budgets and justifying security investments ahead of the 2025 enforcement deadlines. Users often explore alternatives to find a solution that better fits their specific budget, integrates with existing platforms, or offers a different set of analytical features. The search for the right tool is a natural part of the continuous improvement process in managing compliance strategy. When evaluating options, consider tools that offer personalized scenario modeling, clear long-term cost forecasting, and a focus on actionable business intelligence. The goal is to find a solution that not only calculates numbers but also provides the iterative insights needed to adapt your compliance journey and secure your contracting future.
Threat Watch Alternatives
Threat Watch is a sophisticated cybersecurity intelligence solution designed to help organizations assess their cybersecurity health and enhance their defenses against a myriad of evolving cyber threats. By utilizing advanced analytics, it provides a comprehensive evaluation of assets, vulnerabilities, and exposures, making it an invaluable tool for businesses of any size striving to protect their digital environments. Users often seek alternatives to Threat Watch due to factors such as pricing, specific feature sets, or compatibility with existing platforms. When searching for an alternative, it is essential to consider the unique needs of your organization, including the level of protection required, ease of use, scalability, and the responsiveness of customer support. Evaluating these metrics will help ensure that the chosen solution aligns effectively with your cybersecurity objectives.
