Opal44 vs Threat Watch
Side-by-side comparison to help you choose the right product.
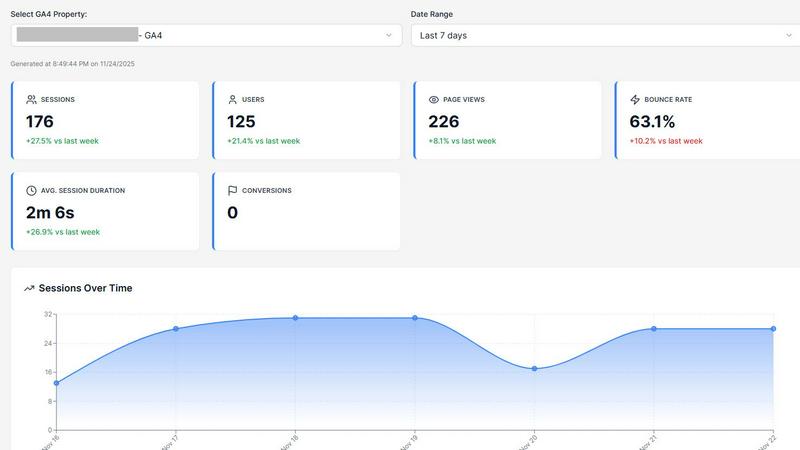
Opal44 transforms your Google Analytics 4 data into clear, actionable insights in everyday language for smarter.
Last updated: March 4, 2026
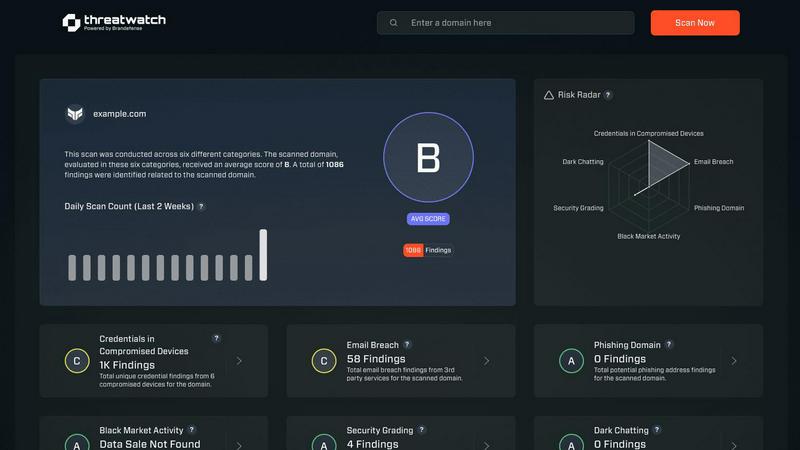
Threat Watch
Quickly gauge your cybersecurity health and gain insights to strengthen your defenses against evolving threats.
Last updated: March 1, 2026
Visual Comparison
Opal44
Threat Watch
Feature Comparison
Opal44
Plain English Insights
Opal44 delivers insights from your GA4 data in simple, everyday language. This feature eliminates the confusion often associated with complex analytics dashboards, allowing users to grasp the meaning behind their website metrics effortlessly.
Conversation-Style Reports
With Opal44, your analytical updates feel like a conversation. The reports are designed to read as if you are chatting with your own analytics guide, ensuring clarity and ease of understanding for users at all levels of expertise.
Smart, Data-Driven Tips
This feature offers tailored suggestions based on your GA4 data. Opal44 analyzes your website traffic patterns and provides actionable recommendations to enhance performance, improve conversions, and support smarter business decisions.
Real-Time Alerts
Opal44 keeps you informed with real-time alerts that notify you of significant changes in your website traffic. Whether it's a spike, drop, or any unusual activity, you can respond promptly to safeguard your online presence.
Threat Watch
Comprehensive Asset Evaluation
Threat Watch provides an exhaustive analysis of your organization's digital assets, identifying vulnerabilities and exposures that could be exploited by cybercriminals. This feature empowers organizations to understand their risk profile comprehensively.
Real-Time Threat Monitoring
With continuous monitoring capabilities, Threat Watch keeps an eye on critical security categories, including compromised devices and breached accounts. This ensures that organizations can detect potential threats as they arise and respond promptly.
Dark Web Intelligence
Threat Watch's dark web content monitoring feature allows organizations to uncover potential threats lurking in hidden corners of the internet. By identifying compromised credentials and sensitive information, businesses can take proactive measures to protect their assets.
Phishing Detection and Prevention
The platform includes robust phishing address tracking, enabling organizations to identify and neutralize phishing attempts before they can cause harm. This feature enhances the security posture by significantly reducing the risk of successful phishing attacks.
Use Cases
Opal44
Small Business Optimization
Small business owners can utilize Opal44 to interpret their website analytics effectively. With straightforward insights, they can identify growth opportunities and make informed decisions to enhance their online strategies.
Marketing Team Collaboration
Marketing teams can benefit from Opal44 by using its conversation-style reports to present data during meetings. This collaborative approach fosters better understanding and alignment on marketing goals and performance.
Digital Agency Reporting
Digital agencies can leverage Opal44 to produce clear analytics reports for their clients. This transparency in reporting not only enhances client relationships but also leads to more productive strategy discussions.
Content Strategy Enhancement
Content creators can utilize Opal44 to optimize their content based on actionable insights. By understanding which pieces resonate with their audience, they can tailor their content strategy to maximize engagement and reach.
Threat Watch
Protecting Sensitive Data
Organizations can leverage Threat Watch to safeguard sensitive customer and business data by continuously monitoring for signs of data breaches and compromised accounts, ensuring compliance and trust.
Enhancing Incident Response
Security teams can utilize the real-time insights provided by Threat Watch to enhance their incident response strategies. By understanding the current threat landscape, they can act swiftly and effectively during security incidents.
Mitigating Phishing Risks
With its phishing detection capabilities, Threat Watch serves as a critical tool for organizations looking to mitigate the risks associated with phishing attacks. By identifying phishing addresses early, companies can protect their employees and customers.
Monitoring Dark Web Activity
Threat Watch enables organizations to stay one step ahead of cyber threats by monitoring dark web activity for compromised credentials. This proactive surveillance allows businesses to take necessary actions before any potential exploitation occurs.
Overview
About Opal44
Opal44 is an innovative AI-powered tool designed to simplify website traffic analysis, particularly for users of Google Analytics 4 (GA4). It transforms complex data into clear, actionable insights, allowing users to understand their website's performance without the confusion of technical jargon. This platform caters to a wide audience, from small business owners and marketing teams to digital agencies and content creators, who seek to make data-driven decisions. Opal44's main value proposition lies in its ability to provide straightforward analytics that are easy to interpret, enabling users to focus on what truly matters—improving their online presence and boosting traffic. With Opal44, you can expect a seamless setup, real-time alerts, and personalized insights that empower you to take control of your website data.
About Threat Watch
Threat Watch is a state-of-the-art cybersecurity intelligence solution meticulously crafted to protect organizations from the dynamic landscape of cyber threats. By harnessing the power of advanced analytics, Threat Watch assesses your organization's assets, vulnerabilities, and exposures to deliver a holistic view of your cyber health. This platform is tailored for businesses of all sizes, from small startups to large enterprises, as it enhances the capabilities of security teams by providing real-time insights that accelerate decision-making and foster effective risk mitigation strategies. With continuous monitoring of critical security categories such as compromised devices, breached accounts, phishing addresses, and dark web content, Threat Watch adopts a proactive approach. This enables organizations to swiftly identify potential threats and prioritize their responses with precision. The main value proposition of Threat Watch lies in its ability to streamline cybersecurity efforts, ultimately bolstering organizational resilience against an increasingly intricate threat landscape. By leveraging Threat Watch, companies can uncover their cybersecurity health rapidly and stay ahead of emerging threats, ensuring a safer digital environment for their operations.
Frequently Asked Questions
Opal44 FAQ
How does Opal44 ensure data security?
Opal44 prioritizes your data security by keeping your GA4 data safe and secure. The platform does not sell or share your information, ensuring that your data remains yours at all times.
What is the setup process for Opal44?
Setting up Opal44 is quick and straightforward. Users can securely connect their GA4 account without needing any coding skills, allowing them to start receiving insights in just a couple of minutes.
Can I try Opal44 before committing to a plan?
Yes, new users can take advantage of a 7-day free trial that includes 50 actions. This allows users to explore Opal44's features and see the benefits firsthand before choosing a subscription plan.
What types of support does Opal44 offer?
Opal44 provides various support options, including email support and priority assistance for professional and agency plans. Their dedicated customer service team is available to help users make the most of their analytics experience.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for businesses of all sizes, from small startups to large enterprises, providing tailored solutions to enhance cybersecurity preparedness across various sectors.
How does Threat Watch monitor compromised devices?
Threat Watch continuously scans and evaluates devices connected to your network, identifying any that may have been compromised by malware or unauthorized access, ensuring swift remediation actions.
Is Threat Watch suitable for organizations with limited cybersecurity resources?
Yes, Threat Watch is ideal for organizations with limited resources, as it streamlines cybersecurity efforts and provides actionable insights that empower teams to make informed decisions quickly.
How does Threat Watch help improve overall cybersecurity health?
By offering comprehensive asset evaluations, real-time monitoring, and dark web intelligence, Threat Watch equips organizations with the tools needed to understand and enhance their cybersecurity posture effectively.
Alternatives
Opal44 Alternatives
Opal44 is an innovative tool designed to provide AI-powered insights into website traffic, leveraging Google Analytics 4 to distill complex data into simple, actionable English. As part of the business intelligence category, Opal44 aims to empower users by removing jargon and making analytics accessible to all. Users often seek alternatives to Opal44 for various reasons, including cost considerations, specific feature requirements, or the need for compatibility with different platforms. When selecting an alternative, it's essential to evaluate the ease of use, the level of customer support, and the ability to tailor insights to unique business needs. Finding a tool that aligns with your objectives can significantly enhance decision-making and drive growth.
Threat Watch Alternatives
Threat Watch is a sophisticated cybersecurity intelligence solution designed to help organizations assess their cybersecurity health and enhance their defenses against a myriad of evolving cyber threats. By utilizing advanced analytics, it provides a comprehensive evaluation of assets, vulnerabilities, and exposures, making it an invaluable tool for businesses of any size striving to protect their digital environments. Users often seek alternatives to Threat Watch due to factors such as pricing, specific feature sets, or compatibility with existing platforms. When searching for an alternative, it is essential to consider the unique needs of your organization, including the level of protection required, ease of use, scalability, and the responsiveness of customer support. Evaluating these metrics will help ensure that the chosen solution aligns effectively with your cybersecurity objectives.
