Fusedash vs Threat Watch
Side-by-side comparison to help you choose the right product.
Fusedash continuously transforms raw data into clear dashboards so your team can act and improve.
Last updated: March 4, 2026
Threat Watch
Quickly gauge your cybersecurity health and gain insights to strengthen your defenses against evolving threats.
Last updated: March 1, 2026
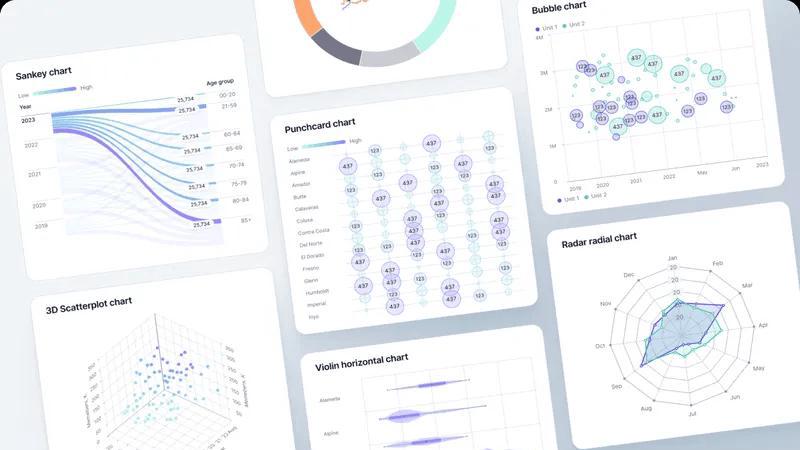
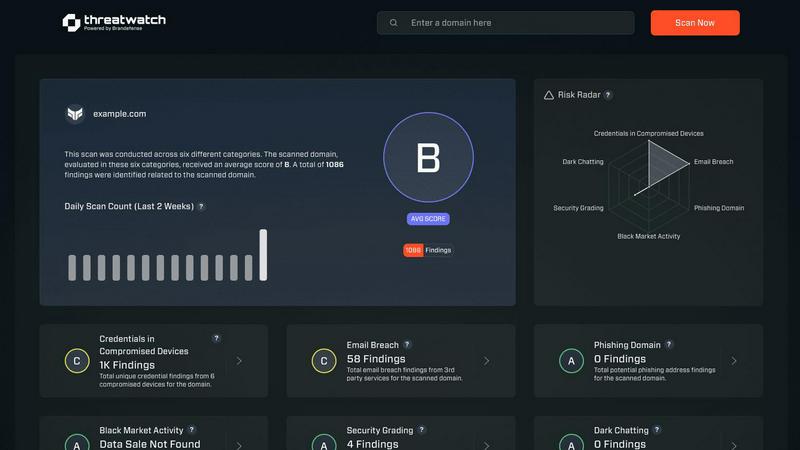
Visual Comparison
Fusedash
Threat Watch
Feature Comparison
Fusedash
Unified AI Visualization Workspace
Fusedash consolidates the entire data storytelling workflow into one cohesive environment. Instead of juggling separate tools for dashboards, charts, maps, and reports, teams can build all these views from the same connected dataset. This eliminates redundant work and ensures consistency. You can start with a standalone AI-generated chart for a quick insight and then seamlessly incorporate it into a broader, real-time monitoring dashboard or a detailed narrative report, creating a continuous loop of insight generation and sharing.
AI Chart Generator
This feature accelerates the initial step of data exploration by allowing users to generate clear, effective visuals from their data in minutes. Simply upload a CSV or connect an API, and use AI assistance to pick the optimal chart type, apply relevant comparisons, and refine labels. These charts serve as foundational building blocks that can be iteratively improved and reused across multiple dashboards and reports, ensuring visual consistency and saving significant time in the report-building cycle.
Contextual Storytelling & Reporting
Fusedash recognizes that dashboards alone often lack narrative context. Its storytelling feature allows teams to combine performance charts and KPIs with written analysis, annotations, and insights. This creates a complete, decision-ready report that explains not just what changed, but why it matters and what the proposed next steps are. This iterative reporting process reduces misalignment and ensures that every data presentation drives toward actionable conclusions and continuous strategic refinement.
Smart AI Data Chat
Embedded directly into the platform, the AI Chat function acts as an always-available data assistant. Users can ask questions about their data in plain language, explore breakdowns by segment or region, and receive intelligent suggestions for relevant metrics or visualizations. This feature democratizes data access, allowing non-technical team members to engage in an iterative exploration cycle, turning their questions directly into shareable, interactive views that fuel ongoing analysis and discussion.
Threat Watch
Comprehensive Asset Evaluation
Threat Watch provides an exhaustive analysis of your organization's digital assets, identifying vulnerabilities and exposures that could be exploited by cybercriminals. This feature empowers organizations to understand their risk profile comprehensively.
Real-Time Threat Monitoring
With continuous monitoring capabilities, Threat Watch keeps an eye on critical security categories, including compromised devices and breached accounts. This ensures that organizations can detect potential threats as they arise and respond promptly.
Dark Web Intelligence
Threat Watch's dark web content monitoring feature allows organizations to uncover potential threats lurking in hidden corners of the internet. By identifying compromised credentials and sensitive information, businesses can take proactive measures to protect their assets.
Phishing Detection and Prevention
The platform includes robust phishing address tracking, enabling organizations to identify and neutralize phishing attempts before they can cause harm. This feature enhances the security posture by significantly reducing the risk of successful phishing attacks.
Use Cases
Fusedash
Streamlining Executive & Board Reporting
Leadership and board members need a consistent, high-level view of organizational health without getting lost in data noise. Teams can use Fusedash to build a centralized executive dashboard with defined KPIs, which is then used as the single source for all reporting. The storytelling feature allows analysts to add monthly commentary and context directly alongside the charts, creating a polished, narrative-driven report package that evolves each cycle, ensuring leaders always have the latest, most coherent story.
Unifying Marketing Campaign Analysis
Marketing teams often pull data from numerous platforms (social, web, email), leading to fragmented analysis. With Fusedash, they can connect all data sources into one workspace. They create a master dashboard for real-time campaign monitoring, use the AI chart generator for quick ad-hoc analysis of specific channels, and employ storytelling to compile weekly performance reports that highlight wins, learnings, and iterative adjustments for the next campaign cycle, keeping the entire team aligned.
Operational & Regional Performance Monitoring
For operations or sales teams managing multiple locations or regions, Fusedash's mapping and filtering capabilities are essential. They can build an interactive map view to monitor KPIs like sales volume or support tickets geographically. Drilling down into a specific region reveals a tailored dashboard for that area's manager. This creates a continuous feedback loop where national trends and local insights inform each other, driving iterative improvements across all operations.
Democratizing Data for Non-Technical Teams
Departments like HR, Finance, or Customer Success may rely heavily on analysts for reports. Fusedash's AI Chat and reusable dashboard templates empower these teams to ask their own data questions and access pre-built, trustworthy views. A customer success manager can quickly check client health scores, or an HR business partner can track hiring funnel metrics, fostering a culture of self-service, data-informed decision-making that improves iteratively as teams learn what metrics matter most.
Threat Watch
Protecting Sensitive Data
Organizations can leverage Threat Watch to safeguard sensitive customer and business data by continuously monitoring for signs of data breaches and compromised accounts, ensuring compliance and trust.
Enhancing Incident Response
Security teams can utilize the real-time insights provided by Threat Watch to enhance their incident response strategies. By understanding the current threat landscape, they can act swiftly and effectively during security incidents.
Mitigating Phishing Risks
With its phishing detection capabilities, Threat Watch serves as a critical tool for organizations looking to mitigate the risks associated with phishing attacks. By identifying phishing addresses early, companies can protect their employees and customers.
Monitoring Dark Web Activity
Threat Watch enables organizations to stay one step ahead of cyber threats by monitoring dark web activity for compromised credentials. This proactive surveillance allows businesses to take necessary actions before any potential exploitation occurs.
Overview
About Fusedash
Fusedash is an AI-powered data visualization platform designed to break the cycle of manual, inconsistent reporting and empower teams with a single source of truth. It acts as a unified workspace where organizations can connect their data once—from CSVs, APIs, or databases—and then continuously transform it into clear, actionable insights. The platform is built for teams tired of conflicting data stories and rebuilding the same logic across disconnected tools like spreadsheets, basic chart builders, and presentation software. Its core value proposition is consistency and efficiency: you define your key metrics and KPIs once, and then reuse those trusted definitions across every dashboard, chart, map, and narrative report. This iterative approach ensures everyone, from leadership to marketing to operations, is aligned on the same numbers, fostering trust and enabling faster, data-driven action. Fusedash goes beyond static monitoring by integrating AI features like natural language data chat and smart visualization assistance, making data exploration an ongoing, accessible process. It turns raw data into a dynamic, shared asset that drives continuous improvement, helping teams not only see what's happening in real-time but also understand why by drilling down into the underlying trends and segments.
About Threat Watch
Threat Watch is a state-of-the-art cybersecurity intelligence solution meticulously crafted to protect organizations from the dynamic landscape of cyber threats. By harnessing the power of advanced analytics, Threat Watch assesses your organization's assets, vulnerabilities, and exposures to deliver a holistic view of your cyber health. This platform is tailored for businesses of all sizes, from small startups to large enterprises, as it enhances the capabilities of security teams by providing real-time insights that accelerate decision-making and foster effective risk mitigation strategies. With continuous monitoring of critical security categories such as compromised devices, breached accounts, phishing addresses, and dark web content, Threat Watch adopts a proactive approach. This enables organizations to swiftly identify potential threats and prioritize their responses with precision. The main value proposition of Threat Watch lies in its ability to streamline cybersecurity efforts, ultimately bolstering organizational resilience against an increasingly intricate threat landscape. By leveraging Threat Watch, companies can uncover their cybersecurity health rapidly and stay ahead of emerging threats, ensuring a safer digital environment for their operations.
Frequently Asked Questions
Fusedash FAQ
What types of data sources can I connect to Fusedash?
Fusedash is built for flexibility in your data integration cycle. You can start immediately by uploading CSV or Excel files. For live, updated data, you can connect directly to various business applications via their APIs. The platform is also designed to combine multiple datasets—like your internal sales data with public demographic information—into a single, coherent view for richer analysis, all within the same iterative workspace.
How does Fusedash ensure data consistency across reports?
Consistency is a core, cyclical principle of Fusedash. You define your key metrics, calculations, and business logic (like "Monthly Recurring Revenue" or "Customer Churn Rate") centrally in the platform as reusable data models. Whenever you or a colleague builds a new dashboard, chart, or report, you select from these pre-defined metrics. This guarantees that every view across the organization calculates numbers the same way, creating a single, evolving source of truth.
Is the AI Chart Generator suitable for complex data analysis?
Yes, the AI Chart Generator is designed as a starting point for both simple and complex datasets. It assists in the iterative process of visual exploration by recommending the most effective chart type for your data structure (e.g., time series, comparisons, distributions). You maintain full control to then apply filters, add comparisons (like month-over-month growth), and refine the visualization, making it a powerful tool for accelerating the initial insight discovery phase before diving deeper.
Can I share dashboards and reports with people outside my company?
Absolutely. Fusedash provides secure sharing options to support collaborative and client-facing cycles. You can generate shareable links to interactive dashboards or export polished, narrative reports as PDFs or presentations. You control the access level, allowing you to disseminate insights to external stakeholders, clients, or partners while maintaining the integrity and consistency of the data story you've built.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for businesses of all sizes, from small startups to large enterprises, providing tailored solutions to enhance cybersecurity preparedness across various sectors.
How does Threat Watch monitor compromised devices?
Threat Watch continuously scans and evaluates devices connected to your network, identifying any that may have been compromised by malware or unauthorized access, ensuring swift remediation actions.
Is Threat Watch suitable for organizations with limited cybersecurity resources?
Yes, Threat Watch is ideal for organizations with limited resources, as it streamlines cybersecurity efforts and provides actionable insights that empower teams to make informed decisions quickly.
How does Threat Watch help improve overall cybersecurity health?
By offering comprehensive asset evaluations, real-time monitoring, and dark web intelligence, Threat Watch equips organizations with the tools needed to understand and enhance their cybersecurity posture effectively.
Alternatives
Fusedash Alternatives
Fusedash is an AI-powered data visualization and business intelligence platform. It helps teams transform raw data from various sources into clear, actionable dashboards and reports, creating a single source of truth for the entire organization. Users often explore alternatives to find a solution that aligns perfectly with their unique needs. This search can be driven by factors like budget constraints, the need for specific integrations, or a desire for different feature sets. The goal is to find a tool that fits seamlessly into their existing workflow and data ecosystem. When evaluating options, consider how a platform ensures data consistency and reduces manual effort. Look for a solution that empowers continuous improvement by making insights accessible and actionable for everyone, not just data specialists. The right tool should evolve with your team's growing analytical maturity.
Threat Watch Alternatives
Threat Watch is a sophisticated cybersecurity intelligence solution designed to help organizations assess their cybersecurity health and enhance their defenses against a myriad of evolving cyber threats. By utilizing advanced analytics, it provides a comprehensive evaluation of assets, vulnerabilities, and exposures, making it an invaluable tool for businesses of any size striving to protect their digital environments. Users often seek alternatives to Threat Watch due to factors such as pricing, specific feature sets, or compatibility with existing platforms. When searching for an alternative, it is essential to consider the unique needs of your organization, including the level of protection required, ease of use, scalability, and the responsiveness of customer support. Evaluating these metrics will help ensure that the chosen solution aligns effectively with your cybersecurity objectives.
