Perkoon vs Phishly
Side-by-side comparison to help you choose the right product.
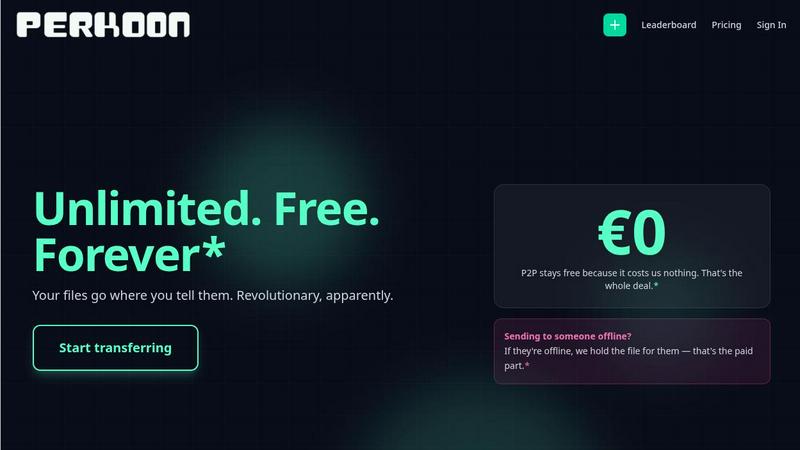
Perkoon enables free, unlimited peer-to-peer file transfers with no signup, ensuring your files stay private and secure.
Last updated: March 4, 2026
Phishly
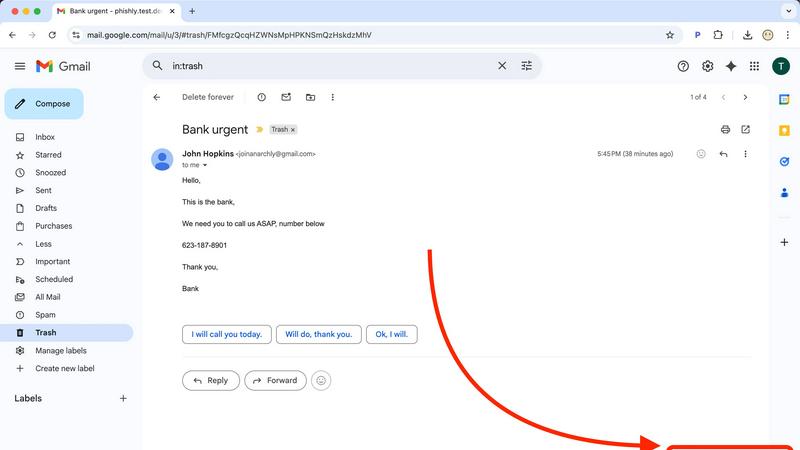
Phishly uses AI to continuously improve your email security by instantly detecting phishing threats.
Visual Comparison
Perkoon
Phishly
Feature Comparison
Perkoon
Peer-to-Peer File Transfer
Perkoon’s flagship feature enables users to transfer files directly between browsers with no size limits. This peer-to-peer technology ensures that files are sent instantly and privately, as the data never touches a central server.
Encrypted Cloud Storage
For situations where the recipient is offline, Perkoon offers secure cloud storage. This feature encrypts files on the server, providing a safe way to hold files until the recipient is available to receive them.
Built-in Automation Tools
Designed for the modern age of AI, Perkoon includes built-in tools that allow automation and interaction with AI agents. This feature ensures seamless integration, making it easier to manage file transfers without manual intervention.
Simple Command-Line Interface
Perkoon provides a straightforward command-line interface (CLI) tool, allowing users to engage with the service programmatically. This feature is perfect for tech-savvy users and applications that require direct file transfer capabilities without a graphical interface.
Phishly
AI-Powered Phishing Detection Engine
At the heart of Phishly is a sophisticated AI engine trained to identify the nuanced hallmarks of phishing attempts. It goes beyond simple spam filters, analyzing email content, headers, and metadata for suspicious domains, grammatical inconsistencies, spoofed sender information, and psychological triggers like urgency or fear. This engine engages in a continuous cycle of learning, iteratively improving its detection capabilities with every scan to stay ahead of emerging threats and provide you with the most accurate risk assessment possible.
Seamless Gmail Integration via Chrome Extension
Phishly integrates directly into your daily workflow with a lightweight and intuitive Chrome extension for Gmail. This feature eliminates the need to switch between applications or copy-paste content. Simply open any email in your Gmail inbox and click the "Scan with Phishly" button. Within seconds, you receive an analysis without ever leaving your email client, making security checks a effortless and habitual part of your email management routine.
Web-Based Tool for Universal Email Analysis
For emails received outside of Gmail or for users who prefer a dedicated portal, Phishly offers a versatile web tool. This platform allows you to paste the full headers and content of any suspicious email—from any client or source—for a comprehensive, instant analysis. This flexibility ensures that no matter where a phishing attempt lands, you have a reliable and consistent method to vet its legitimacy, closing security gaps across your entire digital communication spectrum.
Clear, Actionable Risk Assessment & Explanations
Phishly translates complex threat analysis into simple, actionable intelligence. Every scan results in a clear, color-coded risk rating: Safe, Medium Risk, or High Risk. More importantly, each rating is accompanied by a detailed breakdown explaining why the email received that score, highlighting specific detected indicators like a mismatched "Reply-To" address or deceptive link. This educational component is crucial for user awareness, fostering a cycle of continuous learning and improvement in personal threat recognition.
Use Cases
Perkoon
Creative Professionals
Graphic designers, video editors, and photographers can leverage Perkoon to send large files to clients or collaborators effortlessly. The P2P transfer method allows for quick and hassle-free sharing of high-resolution content.
Remote Teams
Remote teams working on projects can utilize Perkoon to transfer essential documents and files without the burden of account setups or size restrictions. This fosters a collaborative environment free from corporate data handling concerns.
AI Development
Developers creating AI applications can use Perkoon to send datasets or model files securely and efficiently. The built-in automation tools make it easy for AI agents to manage file transfers autonomously.
Educational Institutions
Schools and universities can benefit from Perkoon by allowing students and faculty to share educational materials and resources. The service's privacy features ensure that sensitive information remains protected during transfers.
Phishly
For Individuals Managing Personal Inboxes
Everyday users receive a barrage of emails from banks, retailers, and services, making it easy for phishing attempts to blend in. Phishly acts as a personal security advisor, allowing individuals to instantly check emails claiming to be from their bank, a shipping company, or a social media platform. This proactive habit builds a stronger, more iterative defense against identity theft and financial fraud, turning uncertainty into confident action with every suspicious message.
For Small Business Teams and Remote Workers
Small businesses often lack dedicated IT security staff, leaving employees as the first line of defense. Phishly equips every team member with an easy-to-use tool to verify emails requesting sensitive data, invoice payments, or credential changes. By integrating this check into their workflow, businesses can create a culture of security awareness, continuously improving their collective resilience against business email compromise (BEC) and other targeted attacks without complex training or infrastructure.
For Verifying Urgent or High-Stakes Communications
Phishing attacks frequently use urgency to bypass rational scrutiny. When you receive an email demanding immediate action—like a password reset you didn't request, an urgent wire transfer from a "CEO," or a warning about an expiring account—Phishly provides a critical moment of pause. Scanning the email delivers an objective risk assessment, helping you avoid panic-driven mistakes and ensuring you only act on legitimate, high-priority communications.
For Educational Purposes and Security Awareness Training
Phishly serves as an excellent real-time educational tool. By scanning both obvious and subtle phishing attempts, users can review the detailed explanations of detected risks. This process helps them learn to identify suspicious patterns themselves, such as generic greetings, slight domain misspellings, or unusual tone. This cyclical feedback loop of scan, learn, and recognize fosters continuous improvement in personal cybersecurity hygiene and threat detection skills.
Overview
About Perkoon
Perkoon is a revolutionary file transfer service designed for those who value simplicity and privacy in sharing files. It aims to eliminate the clutter of artificial limits, obligatory sign-ups, and the corporate treatment of personal data. Targeted at anyone who has struggled with traditional file transfer services, Perkoon provides a straightforward solution for transferring files effortlessly. At its heart, Perkoon utilizes peer-to-peer (P2P) technology to allow users to send files directly between browsers when both parties are online, ensuring no size limits and total privacy. For instances when the recipient is offline, Perkoon offers secure cloud storage as a paid feature, which is essential for maintaining the service's sustainability. Unique to Perkoon is its design optimized for the AI age, integrating automation tools and allowing AI agents to interact directly with the service without the need for screen scraping. With a simple command-line interface (CLI) tool available, Perkoon stands out as a powerful, privacy-centric solution for individuals and machines alike.
About Phishly
In the ever-evolving digital landscape, where phishing attacks grow more sophisticated by the day, Phishly emerges as your vigilant, AI-powered sentinel. It is a purpose-built phishing detection platform designed to demystify email security for everyone. Available as a convenient Chrome extension for Gmail and a straightforward web tool, Phishly empowers you to take control of your inbox safety with a single click. The core mission is simple: to provide instant, clear, and actionable risk assessments for any email that raises suspicion. By leveraging advanced artificial intelligence, the platform continuously scans for a comprehensive range of phishing indicators—from subtly spoofed sender addresses and deceptive domains to manipulative urgent language and complex social engineering tactics. This cyclical process of analysis and learning ensures the detection engine is always improving, adapting to new threats as they emerge. Tailored for individuals, remote workers, and small to medium-sized businesses, Phishly delivers enterprise-grade security insights without the associated complexity or cost. It respects your privacy fundamentally by only analyzing emails you explicitly choose to scan, putting you in complete control. With no technical knowledge required and a free-to-use model, Phishly is the definitive tool for achieving continuous improvement in your personal and organizational cybersecurity posture, offering peace of mind in an instant.
Frequently Asked Questions
Perkoon FAQ
Is Perkoon truly free?
Yes, Perkoon offers its peer-to-peer file transfer service for free. This is possible because the P2P technology incurs minimal costs, allowing users to transfer files without financial constraints.
How does Perkoon ensure my files are private?
Perkoon prioritizes user privacy by ensuring that P2P transfers do not pass through its servers. For cloud storage, files are encrypted, and Perkoon cannot access the content being sent.
What happens if my recipient is offline?
If the recipient is offline, Perkoon holds the file in encrypted storage until they are available to receive it. This ensures that file transfers can still occur seamlessly, regardless of online status.
Which browsers are supported by Perkoon?
Perkoon supports Chrome, Edge, and Brave without restrictions. However, users of Firefox and Safari may encounter certain limitations due to browser-specific constraints.
Phishly FAQ
How does Phishly protect my privacy?
Phishly is built on a foundation of user privacy and explicit consent. The platform only analyzes emails that you actively and deliberately choose to scan. When using the Chrome extension, the analysis is performed on the specific email you open and click to scan. We do not access, read, or store emails from your inbox automatically. Your data is processed securely for the sole purpose of providing the phishing risk assessment.
Is Phishly really free to use?
Yes, Phishly is currently free to use. Our goal is to make essential phishing protection accessible to everyone, from individuals to small businesses, helping to build a more secure internet community. We believe in providing this core security service without barriers, supporting a continuous cycle of improvement in user safety and awareness for all our users.
What makes Phishly different from my email's spam filter?
Traditional spam filters operate automatically in the background and primarily catch bulk, low-effort spam. Phishly is a targeted tool for analyzing sophisticated phishing emails that often bypass these filters because they appear to come from trusted sources. It gives you on-demand, deep analysis with clear explanations, focusing on deception and social engineering rather than just bulk content, putting investigative power directly in your hands.
Do I need technical skills to use Phishly?
Absolutely not. Phishly is designed for complete ease of use, requiring zero technical knowledge. The interface is straightforward: either click one button in Gmail or paste text into our website. The AI handles all the complex analysis and presents the results in a simple, color-coded format with plain-English explanations. It's built to empower anyone to make safer decisions instantly.
